Side-channel attacking browsers through CSS3 features
Some people don’t like CSS because it’s not a “real” programing language like JavaScript; other people use CSS to exfiltrate data.
Side-channel attacking browsers through CSS3 features | Security Research - Evonide
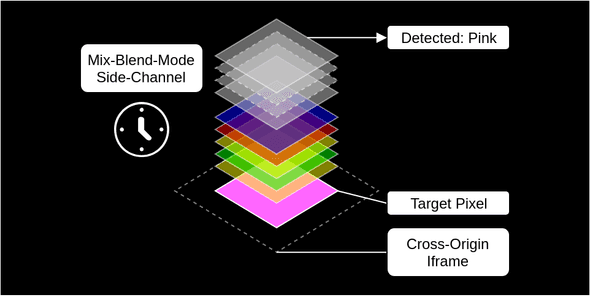
- We (co-)discovered a side-channel vulnerability in browser implementations of the CSS3 feature “mix-blend-mode” which allowed to leak visual content from cross-origin iframes.
- We demonstrate the impact of this vulnerability by showing how visiting a malicious site was enough to de-anonymize Facebook users. In particular, exploitation allowed to leak the profile picture, username and likes of unsuspecting visitors all while requiring no additional user interaction.
- This vulnerability affected major browsers like Chrome and Firefox and was disclosed responsibly.